Cybersecurity experts have warned businesses about malicious email attachments for decades, as it continues to be a common phishing tactic. According to a new report by Barracuda Networks, 45.7% of all scanned HTML files were malicious in March 2023. That means HTML attachment attacks have doubled since May 2022, when that number was only 21%. While HTML attacks are nothing new, the dramatic increase suggests hackers are having more success with them.
Many businesses have transitioned workers back to the office over the past year, though remote work is still popular. While that can increase productivity and job satisfaction, it’s created a less secure working environment. With different home network configurations, less guarded computers, and more casual device usage outside of work hours, there are a lot of weak points in home cybersecurity.
Additionally, many small businesses don’t understand the impact of digital threats fully. If everything has been working as-is for years, it’s easy to assume that will continue to be the case. Yet, once a company falls prey to a cyber-attack, it’s already too late. Stolen data can lead to losing customer trust, reduction in revenue, fines, and potential legal challenges. Like any attack, being careful with email HTML attachments is vital.
How HTML Attachment Attacks Can Trick Users
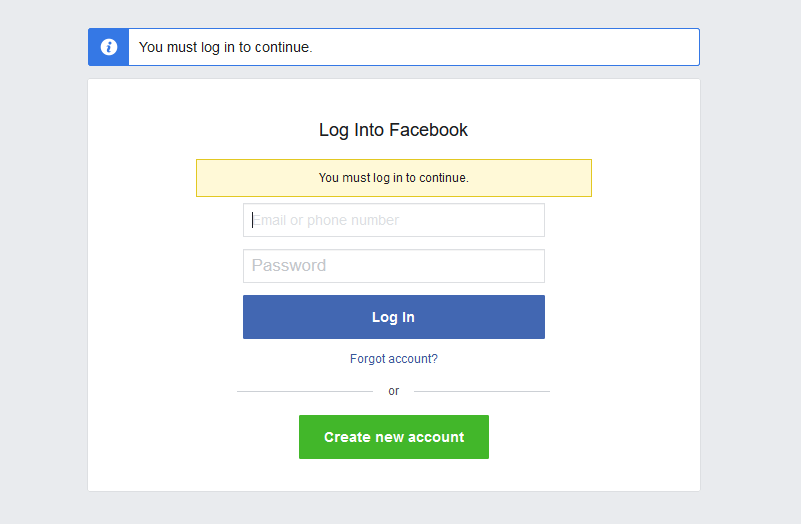
When attached to an email, HTML is a significant threat in the wrong hands. It’s commonly used to redirect users to malicious websites or make fake login pop-ups on the local computer. Both can be very convincing since they copy the real thing, making it easy to be tricked by them. Anything that’s typed into a false login form is recorded and sent to the attacker. That allows them to gain access to personal and business accounts, leading to stolen data and misused services.
Some website redirects may also encourage users to download bigger files that are malware infected. In rare situations, hackers will embed the entire malware script in the HTML file. That method is harder to hide and will often be blocked by email spam filters. They’re just as dangerous as any other type of malware, though, so even if they’re uncommon, people still need to be careful opening any suspicious attachments.
It’s hard for antiviruses and security teams to detect lighter HTML attacks, like website redirects, as they can be more easily encrypted and aren’t the direct threat. One group of attackers even used Morse code as a roundabout way to hide their phishing scheme. IT security can be viewed as an arms race, as once one approach is countered, a new attack method is developed, and the cycle repeats. To keep up, businesses and cybersecurity teams must stay informed of the latest risks and trends.
Take Extra Steps To Protect Workers From HTML Attacks
Like many other threats, HTML attachment attacks require the user to click something before anything can happen. While hackers can use them to inject viruses in rarer cases, most commonly, HTML attachments are used for phishing. That means it requires at least two steps before the damage is done. The first is opening the attachment, and the second is inputting the requested login information.
The best way to protect workers comes from layering multiple strategies. For remote workers, that means requiring additional security such as a VPN, multi-factor authentication (MFA/2FA), device posture checks (DPC), or zero trust network access (ZTNA). The best approach depends on the business and how the staff interacts with their accounts. Office environments should already have better control over their device and network security.
Since clicking the attachment is the source of the problem, teaching good cybersecurity habits will also help keep people safer in the office and at home. It’s easy to get caught up in a work routine, though, meaning mistakes happen. That’s where an IT security team comes in. They can provide solutions that reduce the chance of malicious emails reaching a user’s inbox. Businesses can prevent most HTML attachment attacks by teaching risk awareness, security habits, email protection, and setting up a secure work environment.




