It’s Been a Busy Year for Hackers
We are ¾ of the way through 2019.
Nine months in, ransomware attacks have skyrocketed with attacks on at least 621 US government agencies, healthcare providers and schools.
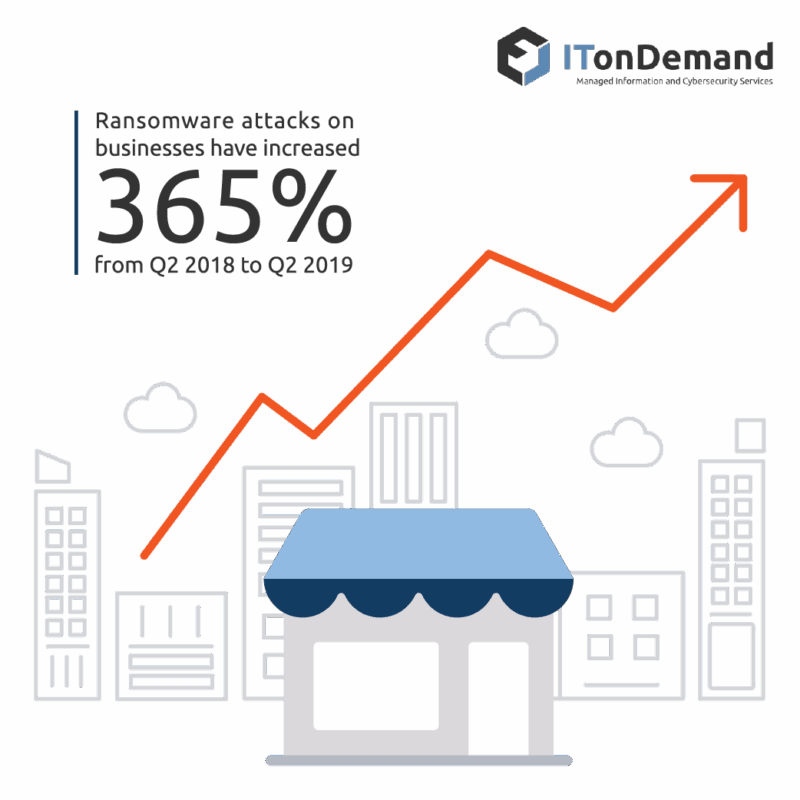
In the private sector, business detections of ransomware rose 365% from Q2 2018 to Q2 2019.
As hackers transition from targeting consumers to primarily businesses and organizations, their work has become significantly more lucrative.
Ransom demands have continued to increase in 2019. The cost of rebuilding systems is often significantly more than the cost of simply paying the ransom. And if one organization is willing to pay, the next may be willing to pay more.
The Industries That Have Seen the Greatest Impact

Government
- The attack on Baltimore left the city’s systems offline for over 3 weeks. By refusing to pay the ransom of $76,000, the city was forced to rebuild its digital systems. This left the city with a hefty $18.2 million estimate. Property transactions, tax, and water billing were all disrupted.
- A trio Florida Cities paid over $1.2 million collectively after ransomware hit Key Biscayne, Lake City, and Riviera Beach in June. In this instance, the governments affected all agreed to pay the ransomware. In the months since the attacks, US mayors have all agreed to not pay ransoms.
- This April, information boards and email were encrypted in an attack on Cleveland/John Hopkins Airport. Both the airport and the Mayor’s office were initially slow to give any details. The city claims to have managed the damage internally with conflicting reports that the FBI was involved.
Healthcare providers
- On October 1st, 2019, DCH Regional Medical Center, Fayette Medical Center and Northport Medical Center were all infected with RYUK ransomware. The hospitals are all a part of the DCH Health System. All affected hospitals were reduced to using pen and paper records and were rerouting incoming ambulances and patients to other nearby hospitals for 10 days.
- PerCSoft, a cloud provider for dental offices, was hit with a ransomware attack that encrypted the patient information for 400 dentists’ offices.
Education
- Similar to the DCH Health System attack, the Rockville Center School District in Long Island, NY was infected with RYUK Ransomware this August. The school district paid close to $100k to have their information decrypted.
- Flagstaff United School District closed for two days following a ransomware attack in September. No details were released on the recovery from the incident.
- In July, Monroe College based in New York City fell victim to an unknown strain of ransomware. The hackers later requested $2 million dollars to decrypt the infected hardware.
The Trends We Can See
Insurance is encouraging hackers
Hackers are receiving payment largely when businesses utilize cyber insurance. This is causing two noticeable trends. The volume of attacks is growing as the practice becomes more lucrative and the ransom amounts themselves are growing, quickly.
Hackers target MSPs
Hackers have also begun targeting managed service providers and IT firms. By doing this, they not only cripple the IT firm but also disable the provider’s clients. This is the case as evidenced by the PerCSoft attack above.
Email and remote desktop protocol are primary vulnerabilities
It is well established that email is the most common vulnerability but any feature that adds access to internal systems is a potential vulnerability. Ransomware like SamSam, CryptON and CrySIS have all been spread through RDP attacks. Hackers can easily find and target organizations by scanning for open RDP connections.
Statistics
- By the end of 2019, ransomware will claim a new victim every 14 seconds.
- Ransomware is expected to top $11.5 billion this year.
- There were 204m ransomware attacks in 2018.
- In 2018, there were 222 new families of ransomware created.
- Ransomware induced downtime costs an average of $8,500 an hour.