Cybersecurity awareness has been an ongoing theme here at ITonDemand, with fake Google Chrome updates being the latest trending threat. Many businesses understand the importance of keeping their software and web browsers updated, as that’s vital to reducing risks. However, hackers are preying on that goal of staying safe by using fake Chrome updates.
Some of these are being spread through hacked websites, with a recent attack campaign running since November 2022. The issue with hacked websites is that official links and buttons redirect users to fake pages. From there, they’re prompted with innocent-looking pages encouraging users to update their Google Chrome by clicking a download link. The malware is loaded onto the downloaded file, and once opened, it’ll install itself on the computer.
What the Latest Fake Chrome Update Does
The latest fake Chrome update looks like a legitimate error message that claims an issue occurred with the automatic updater. Since many people who use Chrome let it update automatically, this approach makes the reason for updating sound more logical. To further convince the user that it’s a safe download, it even suggests that you can wait for the next automatic update.
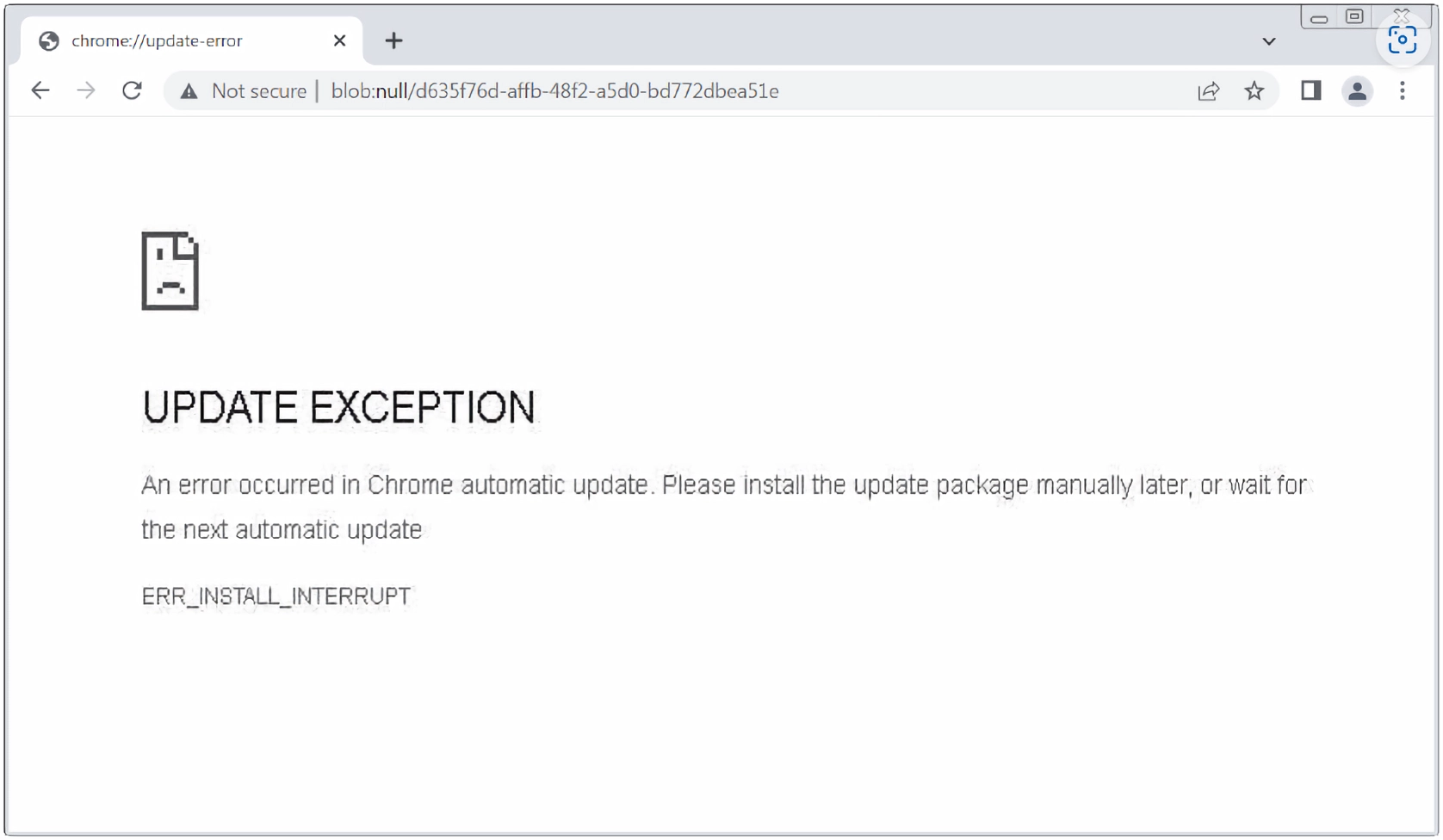
Once downloaded, the user will end up with a ZIP file that has an EXE inside. Once that EXE is activated, it installs a Monero cryptocurrency miner. Unlike some attacks, this is done more passively using computer resources, which can greatly slow it down. What can make this harder to detect is the hacker doesn’t need personal data or file access. Having the crypto miner active is enough to earn them a small amount of money from targets passively.
What Do Other Fake Updates Look Like?
There are a lot of tactics and styles with fake Google Chrome updates. While they come and go out of popularity, hackers have used malicious browser updates for over a decade. While many types of malware will take a more aggressive approach to scare people into downloading them, these attacks don’t always sound as urgent or threatening. That keeps it more on-brand with how companies communicate with customers, making people less likely to notice something is wrong.
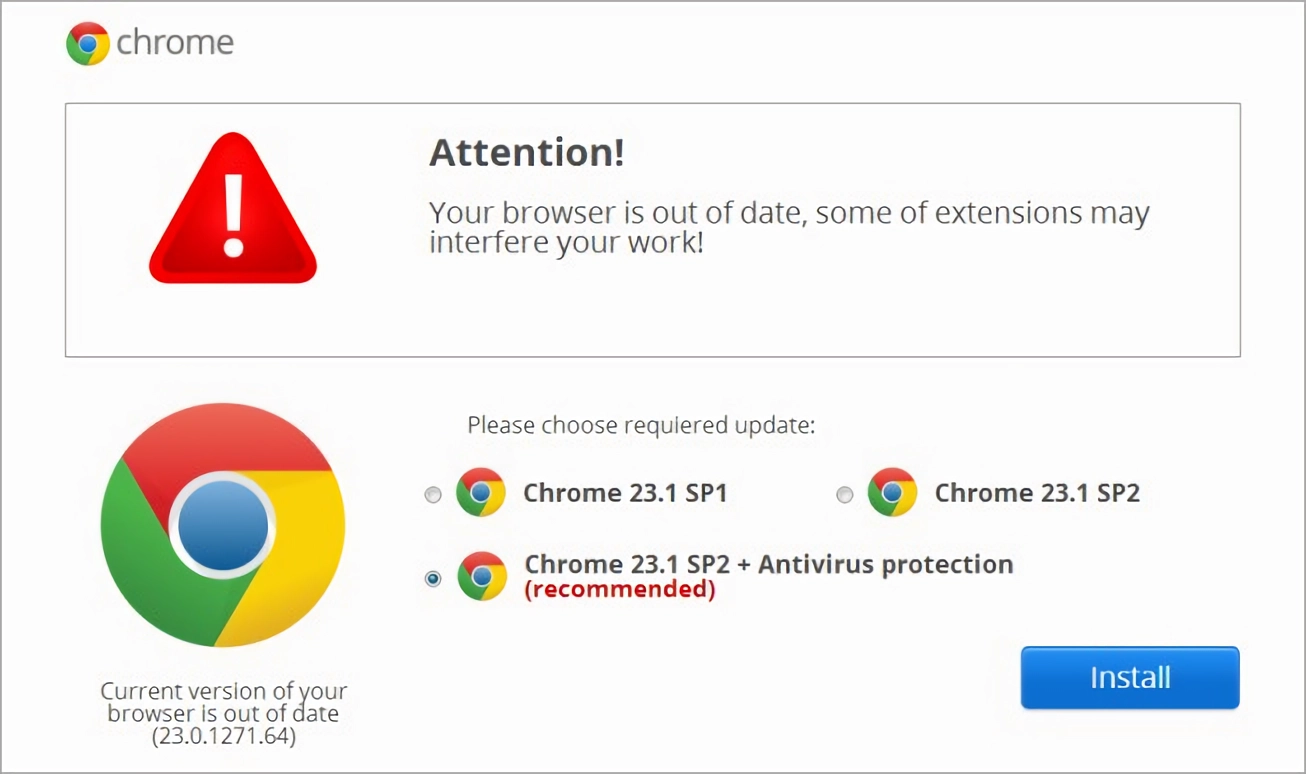
Here are some examples of what a fake Chrome update can look like:
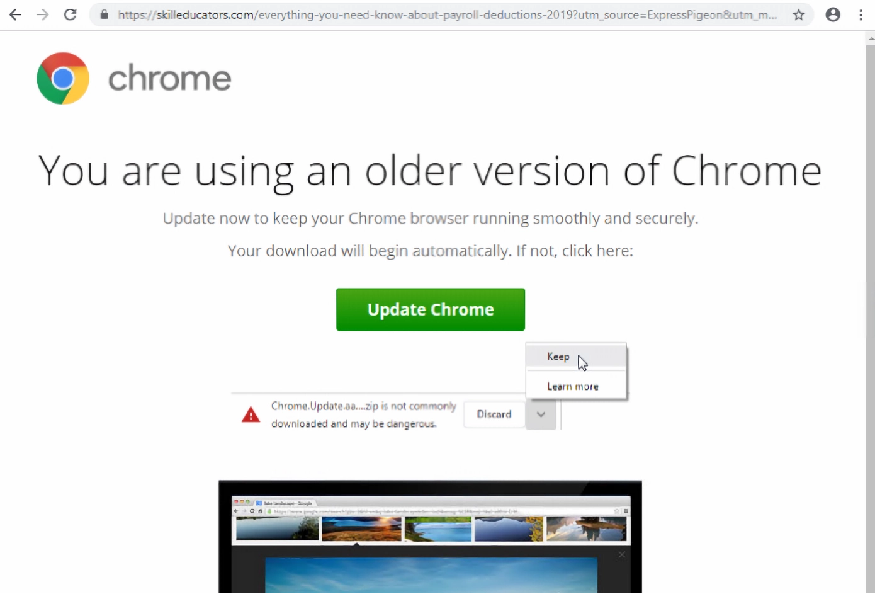
This image comes from a 2020 attack allowing hackers to access users’ devices. It came in two flavors. One targeted a user’s bank accounts, while the other allowed remote access to the device, making it easier to spy on activity and steal information.
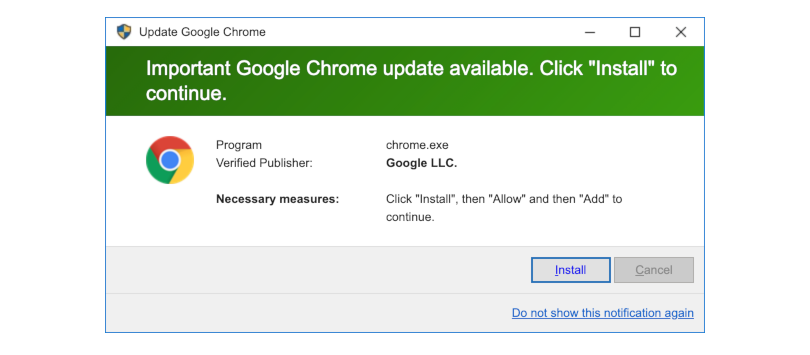
The next one comes from 2-viruses and is a web browser pop-up that copies the Windows 10 style. Since it’s a fake pop-up, it can make the program and verified publisher look official. Clicking install downloads the malicious file but may require the user to open it to activate it.
Lastly, we have an older style fake update page. Compared to the previous two, it looks less official but is still enough to catch some people off guard. Like the others, the goal is to get the user to download and open a file, allowing them to infect the computer.
How To Check for Real Chrome Updates and Spot a Fake
Most of these attacks have web addresses at the top that aren’t connected to Google. Currently, the official website to download Google Chrome is https://www.google.com/chrome/. If you see a different site in your web browser and you’re asked to update it, there’s a high chance that it’s a fake.
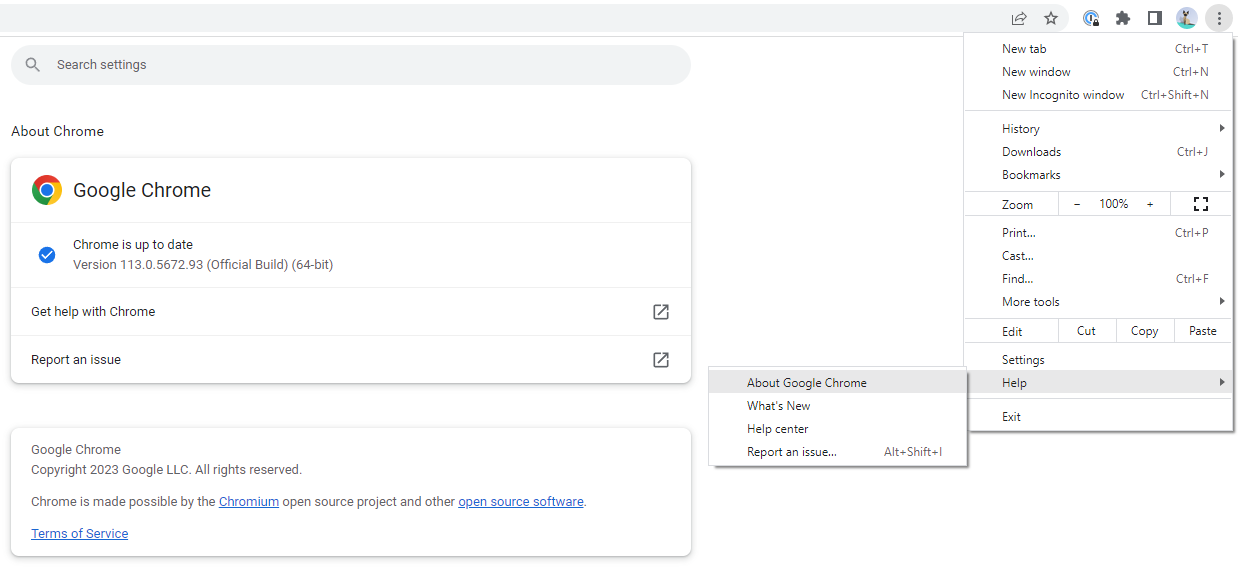
For most people, Chrome will automatically update itself, meaning you won’t see any update prompts in the first place. If Chrome does need a manual update, it’ll happen through the web browser itself, as seen above, and won’t require a separate download.
Ask Your IT Team Before Downloading and Opening Files
Downloading a malicious file doesn’t always mean your computer will be infected immediately. However, once that file is opened, it can activate. The safest thing to do is ask your IT team before you download or access any file found while browsing online. They can also do update management, meaning they’ll ensure Google Chrome, software tools, and devices stay current and don’t require extra work on your end.
If you need help managing your software updates or have other cybersecurity concerns, get in touch with ITonDemand through our contact form or call us at +1 (800) 297-8293